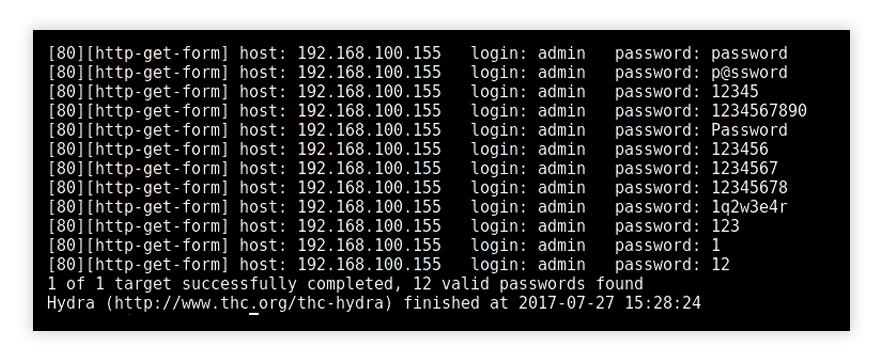
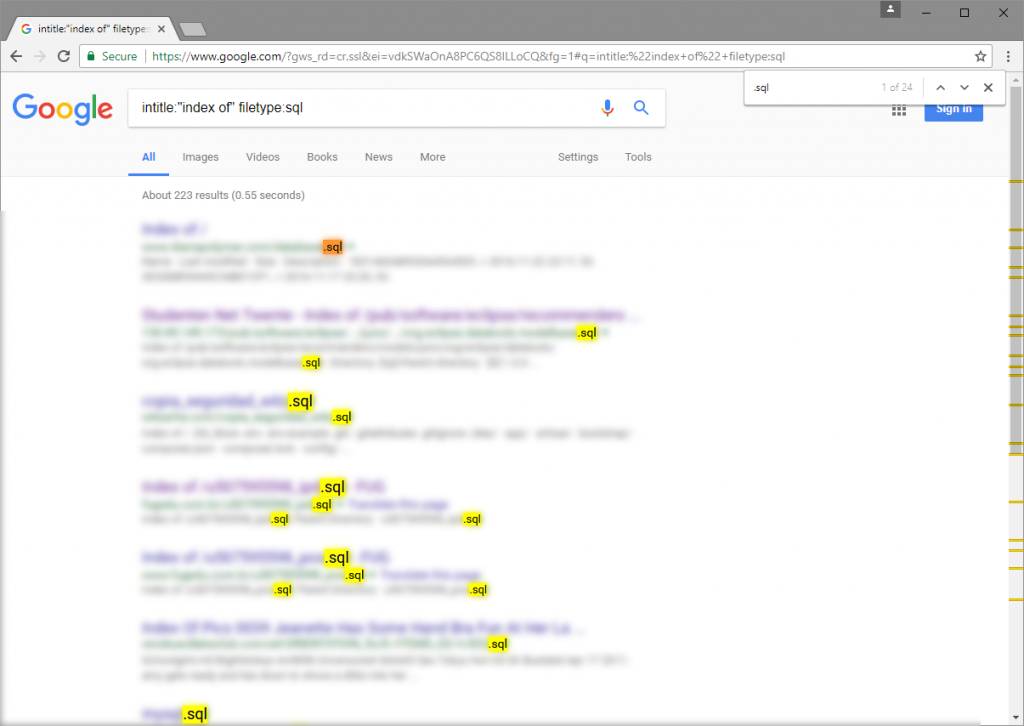
Google Hacking – How to Find Vulnerable Data Using Nothing but Google Search Engine | Objectivity Blog

Hacking: The No-Nonsense Guide: Learn Ethical Hacking Within 12 Hours! (Cyberpunk Programming Series) (Volume 2): University, Cyberpunk: 9781542793674: Amazon.com: Books
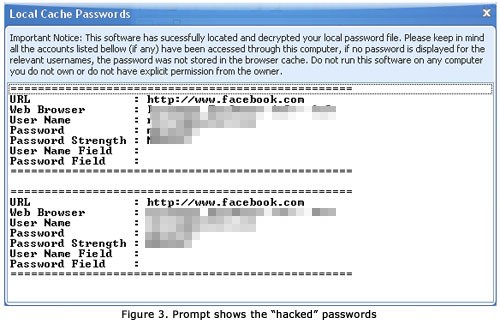
NoHacked: How to avoid being the target of hackers | Google Search Central Blog | Google for Developers